Domain cloning of retailer’s websites has become very popular in the midst of the pandemic and into the peak holiday season, with more than 12,000 suspicious domains related to five big U.S. retailers uncovered over a two-and-a-half-week span from late October into November, according to Mimecast.
In addition, Mimecast uncovered nearly 14,000 suspicious domains related to 20 top global retailers, finding between 53 and 87 such domains registered in one day for a single retailer.
Cyber criminals are also taking advantage of the fact that people are stressed out from “pandemic fatigue” and therefore more susceptible to the lure of what appears to be a legitimate retail site with timely “offers.”
“They will literally will clone a retailer’s site, creating a very similar domain, host it and drive people there,” said Matthew Gardiner, a principal security strategist with Mimecast. “Thinking it’s legitimate, they’ll attempt to log in and give the criminal a credential. Or they’ll attempt to sell them fake goods, or no goods at all.”
While Mimecast did not conduct a similar audit of domain cloning in 2019, Gardiner said he has heard anecdotally from retail customers that the practice is on the rise this year.
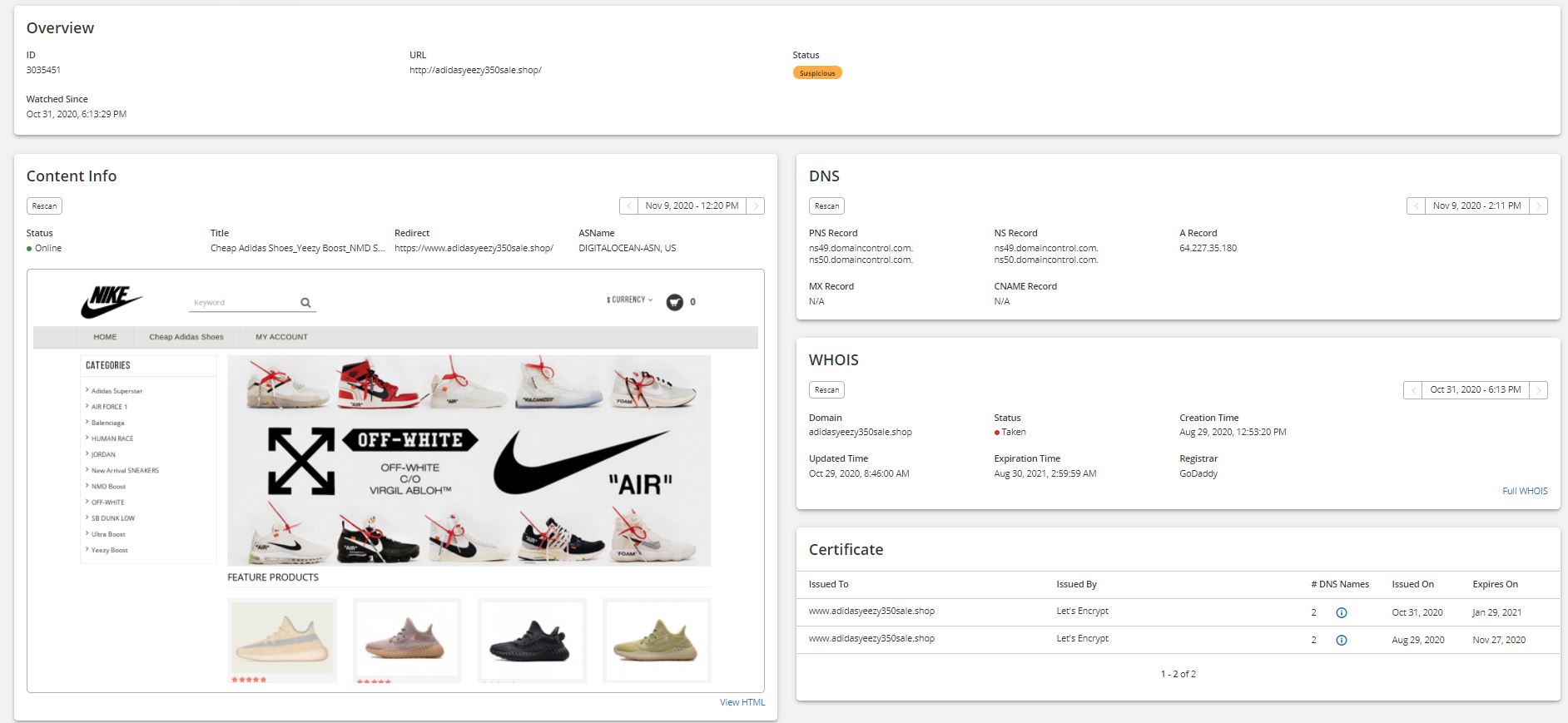
On example unearthed by Mimecast involved a spoofed Adidas site that lured in shoppers, then redirected them in an attempt to sell knockoffs of various footwear brands, including Nike (below). Other times, consumers were lured into fake domains that sought personal or payment information, or redirected them to porn sites.
Gardiner said domain cloning is “somewhat under the radar” partly because smaller retailers and lesser known brands think they’re not vulnerable because it only happens to the bigger players. He said tools used by cyber criminals can simply point at a legitimate domain, clone it and rehost it somewhere else. While some are available on the dark web, demos and tutorials can often be found out in the open on YouTube and Twitter.
“Unfortunately, if they’re not one of those brands, some come to the conclusion it’s not a problem they have to worry about,” he said. “The issue is, they’re not aware of these attacks because the criminals don’t come at the company but to their customers who trust the brand. That’s what makes it more challenging.”
One thing retailers and brands can do to protect themselves, Gardiner said, is to adopt DMARC (Domain-based Message Authentication, Reporting and Conformance). It’s an email authentication protocol designed to give domain owners the ability to protect against unauthorized use such as email spoofing that can draw people into fake domains.
“It’s not widely deployed but it’s emerging quickly,” he said. “It makes it more difficult for unauthorized users to send using your domain.”
Security services can also cut off domain cloning by scouring the web for fake domain registrations that use a legitimate brand. When discovered, they work with the domain registrar to quickly take them down.
“Most legitimate registrars, if someone violates their terms of service by using someone else’s brand without permission, you don’t need to take legal action,” Gardiner said. “You just point it out to GoDaddy and they remove the domain.”
